18 ways CISOs, CTOs and Co-founders can secure their startups in 2022

18 ways CISOs, CTOs and Co-founders can secure their startups in 2022
Cyvatar | 12/21/2021Startups are a prized lot. Venture capitalists and Angel Investors are always scouting for new startups to invest in.
Businesses are seeking to acquire them for building value and growth. Now, it seems, cybercriminals are also equally interested in them.
Yes, these days cybercriminals are increasingly targeting startups and small businesses as much as bigger organizations.
DropBox, Sendgrid, Evernote, Mt.Gox, CodeSpace, you name it, all of them have suffered cyber attacks of one kind or the other. Many of them, within a few months of their companies being launched.
But, most startups are oblivious to this fact.
Most of the startups tend to believe that they are too small and unattractive for them to be attacked. Nothing can be farther from the truth.
There are several reasons why cyber attackers find startups very attractive:
- Many startups lack the necessary awareness and understanding of cybersecurity issues. So, they tend to have weaker defenses that are easy to breach.
- As startups, the focus is on activities like funding, getting the product fit right, building teams, etc. cybersecurity is the last thing on their mind. It does not seem to be a priority and is often deferred or completely ignored.
- Even though small and barely starting, they possess many things that are very valuable. Intellectual property, trade secrets, commercial information like market information, bids, pricing information, customer data, and confidential information that can be accessed.
- Often, many startups are connected to the systems of larger organizations that have stronger cybersecurity protections in place. Cybercriminals use startups as conduits to attack bigger organizations.
What are the most common cyber threats facing startups today?
Depending upon the startup, or the industry vertical, source or types of threats can vary.
Some are existential, while others can cost time, money, and a great deal of effort.
Here are the common major ones:
- IP Theft
Startups are all about translating your ideas into a profitable business. They are built on the strength of ideas, patents, and intellectual property they own.
If you are a tech company, then the major risk is that of IP theft.
- Company Specific Data Theft
If there is one thing that startups are known for, it is their ability for disruption. They have ushered in an entirely new way of doing business, the way products and services are provided.
Many startups hold huge data and confidential information like customer data, passwords, and payment credentials. So, they risk such data being stolen.
- Threat to Financial Transactions
If you are a fintech company, then you are vulnerable to attacks by cybercriminals as huge amounts of money flow through the company system.
Trust is crucial for startups. Marketplace frauds like Data breaches, leaked information, or fraudulent transactions can completely destroy this trust.
- Insider threats
Insider threats can often be a major source of threats for startups.
It can be a negligent employee inadvertently providing access to the company’s data or a disgruntled employee deliberately leaking sensitive information or a founding partner or collaborator who has quit and is now a competitor.
“Just keep in mind that if you want your startup to make a dent in the world, you can’t let hackers make a dent in you.”
– Dan Cowan (Venture Capitalist)
18 Ways That CISOs, CTOs and Co-founders Can Secure Their Startups
Notwithstanding the many challenges, startups can take several steps to put in place a robust cybersecurity setup.
There are many guidelines like the NIST framework for cybersecurity or the CIS Security Controls, V8 that they can use for setting up the cyber defense for their businesses.
However, these guidelines can be a tad heavy for startups. And that’s where Cyvatar’s managed security services can prove to be very handy. Besides making your organization security compliant with important frameworks, we ensure complete online end-to-end security. Try our 30 days, risk-free trial.
However, if you insist on doing it all yourself, we have curated various ways startups can have a more meaningful and cost-effective cyber defense.
Here are the 18 ways CISOs can secure their startups:
1. Cybersecurity Risk Analysis
Different startups face different kinds of risks. They need to know what kinds of threats they face and what kinds of impacts they suffer and what the costs of such attacks are.
In short, they need to know what their threatscape looks like. This will help them choose the most effective solutions.
2. Create a Cybersecurity Strategy
Securing your company against cyber attacks does not mean adopting a few tools and technologies.
It’s important that you have the right kind of expertise and people with knowledge about the regulatory requirements. So, you need to have a clear roadmap.
A fully managed cybersecurity provider not only provides you with a sound security strategy that goes a long way in protecting your organization but helps take your “ever-changing compliance” woes away.
Download this case study to learn how Cyvatar made a huge impact in the security and compliance concerns of AMERICOR for whom the trust of their customer has been utmost. Cyvatar ensured that their customer felt safe.
3. Build A Cybersecurity Culture
It is not enough that you have the necessary tools and technologies in place to secure your organization against cyber attacks.
As people play a vital role and are often the weakest link in cybersecurity, you need to build a culture of cybersecurity in your organization that is empowering all employees.
Here are a few things that you can do without too much effort:
- Communicate and share the Cybersecurity Risk Analysis with your employees. That alerts them to the most destructive threats.
- Create awareness through periodic training in which the founders and executives actually participate.
- Create an easy reporting system. It is often the case that even though the employees are aware of the flaws and mistakes they have committed, they do not report them to the management for fear of retribution.
So it’s important that an easy reporting system is created so that they can report any lapses without fear.
4. Know Your Physical Assets
It is the physical infrastructure like computers, devices, and other hardware that provide the surface for cyber attackers to attack.
These include all the end-user devices, including both portable and mobile devices and network devices.
Startups need to know what physical infrastructure they possess if they have to defend them. So,
- They need to establish and maintain an inventory of their IT physical assets.
- They need to know what authorized assets are there and if there are any unauthorized assets also.
5. Know Your Software Assets
It is important to have a complete inventory of the software the company uses. Cyber attackers are always looking for vulnerable versions of software that can be exploited.
Software that is not updated and patched provides an easy means to mount an attack. Hence:
- Always update and have the necessary patches to your software
- Ensure that only authorized software is supported
6. Secure Configuration Of Hardware & Software Assets
When you buy the hardware and software for your business, the default configuration is set towards ease of deployment and use, rather than security.
Default accounts and passwords and pre-configured settings, unnecessary software, etc can all be easily exploited.
So, it is important that you have a secure configuration process for your hardware and software assets.
Do the following to secure your organization online by fine-tuning certain settings:
- Managing a firewall on end-user devices by blocking certain ports based on specific needs of your organization’s online safety
- Configuring automatic session locking systems on the devices
- Changing the default configuration of the Operating System to better suit your organization’s needs
7. Account & Access Control
One of the easier ways through which cybercriminals gain unauthorized access to your cyberinfrastructure and critical data is through valid user credentials.
There are many ways to gain access to accounts:
- Weak passwords
- Privileged access
- Dormant accounts even after the employee has left the organization, etc.
So, it’s important that credentials are properly monitored, tracked, and managed.
The following specific steps help you secure them:
- Establish and maintain an inventory of all the accounts in the enterprise. This should include both user and administrative accounts
- Maintain access granting & access revoking process
- Use unique passwords
- Disable or delete dormant accounts that are inactive for 45 days or more
- Use the Least Privileged Access policy so that privileged access is given to persons to perform only that particular task
- You can have better control over these matters if you centralize Account Management
- Make Multi-Factor Authentication mandatory for externally exposed applications, remote network access
- Centralize all access control
8. Protect Your Data
Business enterprises hold critical and sensitive data related to their finance, intellectual property, customer-related data, product information, market-related information, or pricing information.
Data breaches are expensive. And the data does not just reside inside the perimeter of your organization. They are everywhere, inside user devices, both desktop & mobile, and shared among many persons and enterprises outside of your organization.
Remote work has made this so pervasive. Hence, it’s important to manage and protect your data throughout its lifecycle.
The following are the steps to manage and protect your data:
- Establish and maintain a proper data management process based on data sensitivity, handling of data, retention limits, and disposal requirements
- Control access permissions to data in local & remote file systems and databases
- Enable data retention. Retain data according to the company’s Data management process
- Encrypt data on end-user devices. You can use tools like Windows BitLocker, Apple Filevault, or Linux dm-crypt
- Document data flows
- Encrypt all data that are stored on devices like computer hard disks, databases, file systems, etc, and are not transferred.
Also, encrypt all data stored on removable media like external hard disks, pen drives, mobile phones, etc.
- Deploy a data loss prevention plan. You can implement an automated tool to identify all sensitive data stored, processed, or shared throughout the enterprise’s system
- Log sensitive data access
- Securely dispose of data
9. Continuous Vulnerability Management
Cyber threats are not one-time threats. The attackers relentlessly pursue targets and are always looking for vulnerabilities in the target’s system to exploit at the slightest opportunity.
Hence, enterprises need to continuously monitor, track and assess their vulnerabilities so that they can take effective preventive and remediation action.
Therefore, it is critically important for startups to:
- Establish a proper vulnerability management process
- Establish and maintain a remediation process
- Patch up all system vulnerabilities
- Patch up all application vulnerabilities
- Scan for vulnerabilities in internally and externally exposed assets
- Remediate detected vulnerabilities
10. Establish & Maintain An Audit Log
Log collection and analysis are vital for detecting threats quickly and taking remedial action. They are the most important and often the only record available to show that an attack has happened.
Many organizations do not take these records seriously. They maintain it only because they are required to do so for compliance purposes. But this is a grave mistake.
This gives an opportunity for cybercriminals to hide their location and the malware so that they can attack at an opportune time.
Therefore, ensure that your startup follows to:
- Establish and maintain a proper log audit and management process
- Collect detailed audit logs
- Conduct audit log reviews
11. Employ Email & Web Browser Protections
Web browsers and email are like the front door and the key. They are the first entry point for all the data in your organization.
Since every kind of organization uses them for interaction within and outside the organization, they form the primary target for attackers.
You can use it to entice users to part with sensitive data or share their credentials so that hackers gain access to the organization’s systems and data.
The following steps help you secure them:
- Ensure use of only fully supported browsers and email clients
- Restrict unauthorized browser and email clients
- Maintain and enforce network-based URLs
12. Build Cyber Resilience
It is not enough to keep data confidential and maintain its integrity. It should also be easily available when needed for business decision-making.
Attackers may often lock up your data or tamper with them. A data recovery plan helps you retrieve such lost data. It is crucial for the recovery of your company from an attack.
- Establish and maintain a data recovery plan
- Do automated backups
- Test data recovery
13. Security Awareness & Skills Training
Your cybersecurity is as good as the people in your organization. No matter whatever defenses you may put in place, if people are not aware of them or do not follow them, such defenses are useless.
Hence, there is a need to create awareness among them and also enable them to practice cybersecurity.
- Creating an awareness training program for people to recognize the various types of attacks like ransomware, phishing attacks, malware, and social engineering
- Carve out budgets for industry certifications in cybersecurity and unlock learning agility in your organization
- Train people on authentication best practices and data handling best practices and define standard operating procedures
- Create a proper reporting system
14. Secure Your Application Software
For many product startups, their own apps are their business, and failure to protect these apps means failure of the business. Also, startups use 3rd party applications to provide the interface for users to access and manage data. Any flaws in them can expose your organization to cyberattacks.
Such flaws may be due to faulty design, coding mistakes, weak authentication, etc.
Steps to address such app vulnerabilities:
- Develop a process to address software vulnerabilities
- Analyze software security vulnerabilities
- Use up to date third-party software components
- Implement code level security checks
15. Service Provider Management
In our globally connected digital world, most businesses depend on third-party vendors and partners to manage their data or for core functions. This is much more so in the case of startups.
Also, data and privacy protection laws like HIPAA, FFIEC, etc require that such third-party service providers are also protected.
- Maintain an inventory of third-party service providers
- Put in place a service provider management policy
- Ensure that contracts with such third-party providers include security requirements
- Monitor service providers
- Securely decommission service providers
16. Pen Testing
It is not enough that a cybersecurity mechanism has been put in place and the right tools and technologies are deployed. It is not good enough to only do a pen test once a year as business environments are rapidly changing. Nothing will be the same by the next morning, let alone the next year and that’s why periodic pen testing should form a part of your overall vulnerability management program.
So, it’s important to perform penetration testing to ascertain whether the defenses are working properly or not.
They can also reveal weaknesses in processes such as incomplete configuration management or end-user training.
Penetration testing is different from vulnerability testing. Vulnerability testing just identifies the gaps and weaknesses.
However, penetration testing further probes to what extent an attacker can exploit such weaknesses and what could be potential impacts on businesses.
Some points to consider while going for penetration testing:
- Put in place a system for periodic penetration testing
- Perform periodic penetration testing
- Fix any issues that emerge out of penetration testing
17. Prepare For Failure
Despite your best efforts, sometimes, the defenses may fail. So, you need to prepare for such eventualities.
Quick points to help you prepare for such eventualities:
- It’s important to know your obligations under the various regulations in case of a cyber attack
- Notify enforcement agencies, regulators, and customers about the data breach
- Quickly move into remediating the situation
- Conduct all internal communication as much as possible, through an alternative communication system
- Explain the situation to customers
18. Transparency
This may sound cliche, however, being transparent and open is a great way to secure your startup from any possible security breach.
The following are a few of the scenarios and ways how transparency makes a huge difference:
- It is very important that you come clean on any data breaches. The more things are kept in the dark, the more the damage
- An open discussion can offer useful insights regarding the cybersecurity you have and what needs to be done to further strengthen it
- An angry customer looking for better clarity on some specific issues always welcomes transparency and openness
- Most importantly, it builds trust and confidence in your investors
The Benefits Of Embracing Cybersecurity For Startups
Much like immunization in infancy affords protection against public health hazards, the benefits of adopting a cybersecurity framework are quite obvious:
- Helps prevent reputational damage leading to loss in revenue and arrests customer churn
- It speeds up sales cycle and your organization can sell more as consumers feel safe with secure checkouts
- Builds trust and confidence in your investors
- Helps you protect your startup against potential cyber attacks that can derail your business
- It is much easier and cheaper to start building cybersecurity for your organization right at the beginning
Be Smarter. Find The Right Partner Who Can Make It Easier & Safer For You
It is easier said than done that startups need to embrace cybersecurity. But doing so will still be a challenge for most of them.
Most startups, as already noted, lack sufficient resources, financial, technical, and human resources for setting up a cybersecurity system.
On top of that, there is this challenge of complying with a plethora of regulatory standards, regulations, and laws. Most startups can not afford a CIO or a CISO. Even if they manage to have one, he/she alone can not manage the whole thing single-handedly. The CISOs need a team of experts and skilled personnel to secure their SMBs and well-funded startups.
“Cyvatar helped us find, prioritize and close vulnerabilities that could potentially otherwise be exploited. Our threat detection and mitigation are now fully automated, and our CEO cites our strong cybersecurity posture as a key advantage and growth enabler.”
DANIEL AKIVA
CYBERSECURITY ADVISOR, AMERICOR
It would be a smart idea for a startup to tie up with a trusted and strategic partner like Cyvatar, that can provide affordable cybersecurity for startups.
Cyvatar is one of the first companies to offer an affordable subscription model for its managed cybersecurity services. A single monthly subscription unlocks a whole set of services across the board. You can contact Cyvatar’s cybersecurity experts to learn more about our managed monthly subscription-based services.
You can explore how Cyvatar is helping startups beef up their cybersecurity by looking into the experience of one of our startup clients.
The good news is; Cyvatar Freemium offers you a risk-free option to kickstart your startup’s security journey with cyber basics like a free CIS assessment and cybersecurity policies. Cancel anytime, but you won’t :)
Cyvatar’s Freemium Membership includes:
- FREE monthly external vulnerability scan
- FREE CIS Assessment (average cost $15K-$100K!)
- Downloadable Cybersecurity Policies
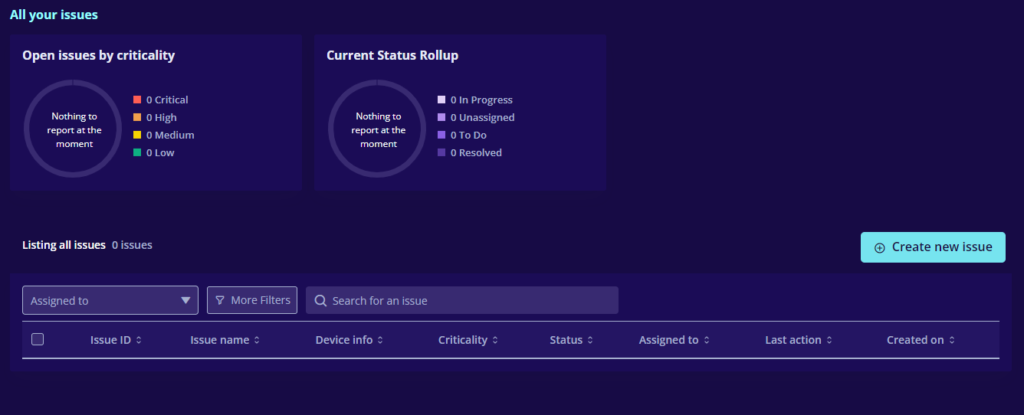
- Business Risk (GRC) Tool
