What is the weakest link in cybersecurity? [Still in 2024]

What is the weakest link in cybersecurity? [Still in 2024]
Cyvatar | 12/06/2021People are the weakest link in the cybersecurity Chain
More and more cybersecurity professionals and CISOs across industries are waking up to an ugly reality: that people within their organizations pose the gravest threat to their cybersecurity and hence, are the weakest link in cybersecurity.
To keep ahead of the ever-evolving challenge of cyber threats, hacking, phishing, credential theft, ransomware, malware attacks, and other cybercrimes, the top leadership of companies and organizations is mainly focused on external threats.
They invest heavily in advanced software and other tools and technologies to deter such attacks.
But they often overlook the fact that the biggest threat lies within their organizations. Consequently, employees, trusted business partners, vendors, and contractors intentionally or inadvertently leaking sensitive information are fast emerging as the biggest threat to an organization’s IT security.
Who is an insider? And what is the impact of an insider threat on businesses & organizations?
The National Institute of Standards & Technology Special Publication NIST 800-53 defines an Insider as “any entity with authorized access… that has the potential to harm an information system or enterprise through destruction, disclosure, modification of data, and/ or denial of service.”
So, any employee, or a former employee/s, third party vendors or a trusted business partner- people with legitimate access to an organization’s networks, systems, digital assets, and sensitive information are considered as Insiders and the leak of such data, data theft, tampering or destruction of data intentionally or unintentionally by them is known as ‘Insider Threat.’
These threats are very real and are growing in numbers and are more frequent in recent years. Damages due to such attacks can be huge.
According to the 2020 cost of insider threats global report prepared by the Ponemon Institute, Insider Threats increased by a whopping 47% between 2018 and 2020. The number of incidents increased from 3200 to 4716 incidents per year.
Also, the report estimated the total average cost of such attacks to be $11.45 Million.
In addition to financial losses, the companies may also suffer the loss of business reputation, loss of customer trust, fall in the price of its shares, hefty regulatory fines, etc. The report says that it takes nearly 77 days to contain a threat.
More worryingly, such threats are hard to detect and are a challenge to the security leadership of companies and organizations.
Hence, people are considered to be the weakest link in the cybersecurity chain.
These insider threats could be found in various forms. Let’s take a look at the different forms of internal threats that can persist.
Types of insider threats
Insider threats can either be intentional or unintentional. Generally, they fall into these 3 categories:
1. Negligent or inadvertent employees:
Most employees do not have any malicious intent but can cause a data breach because they are just casual or careless and can unintentionally leak sensitive data or information.
Several studies point out that nearly 62% of Insider Threats are due to such negligent or careless employees and as such they present a real danger.
Unsuspecting employees may commit the mistake of opening a Phishing email or downloading content that may contain malware, or sharing information and documents with the wrong persons, or may even be tricked into providing sensitive information without realizing it.
Negligence of employees could also lead to credential theft.
Credential theft occurs when a user’s credentials have been obtained unknowingly from such users by malicious attackers to gain access to an organization’s network and steal critical data.
Stolen credentials are a persistent problem and pose a grave threat to an organization’s information security.
CASE 1: Something as innocuous as not updating security software as the following illustrates:
In May 2017, a North Korean hacker collective called Lazarus unleashed Wannacry, a crypto-ransomware (malware used by cybercriminals for extorting money) attack by targeting computers using a vulnerability in Microsoft Windows operating system.
The attack lasted for 4 days and infected around 2,30,000 computers across the world.
The attackers took the victim’s data hostage and demanded payment in Bitcoins. They threatened to wipe out the data completely if the users didn’t make the payments.
The impact was felt worldwide and losses were estimated to be $4 billion.
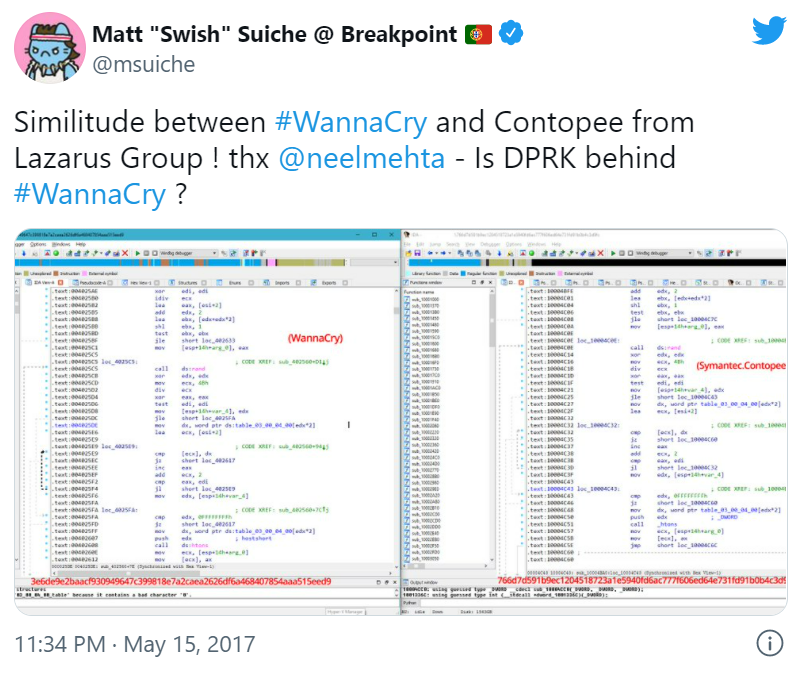
Microsoft had released a security patch protecting users against this just 2 months before the attack. However, many individuals and organizations had not updated the software and fell victim to the attack.
CASE 2: Financial losses due to credential theft
According to the Ponemon Institute Report on Insider Threats, 14% of Insider Threats globally are due to credential thefts and are the costliest per incident.
Credential thefts happen through:
1. Phishing
fraudulent communications sent via emails that appear to come from genuine sources. The purpose is to steal sensitive information like login information or implant malware on the victim’s machine.
2. Social Engineering
Here, the criminal actors fool the victims to part with their credentials or sensitive data by impersonating someone in your organization.
The following case study is a classic example of something as casual as credential theft leading to huge financial losses.
In July 2020, hackers gained access to 130 Twitter accounts with at least a million followers to promote a Bitcoin scam.
Some of the prominent personalities’ hacked accounts included Barack Obama, Elon Musk, Jeff Bezos, Michael Bloomberg, and several others.
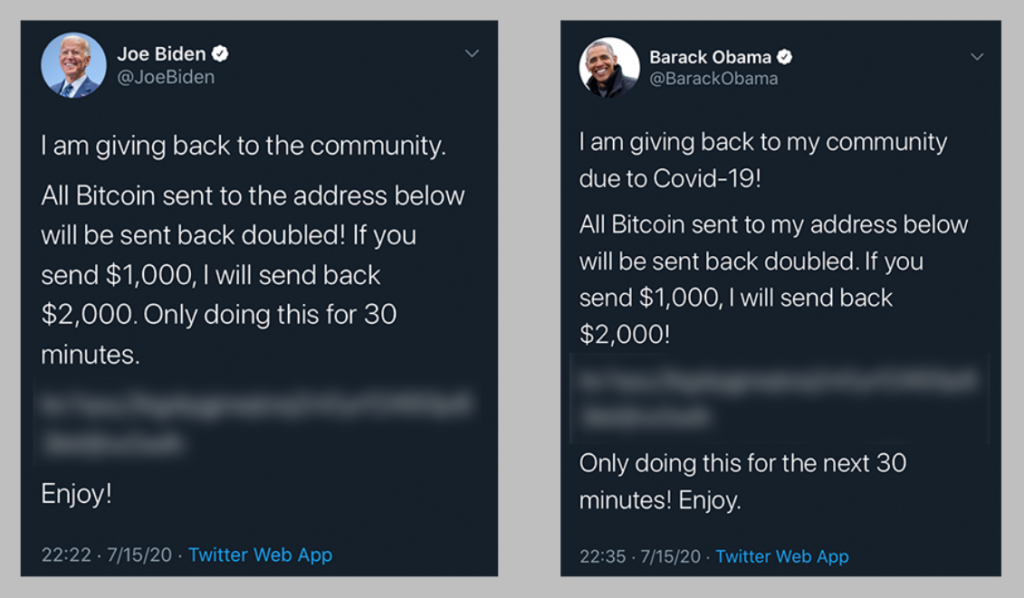
Hackers using spear Phishing (targeting specific individuals in an organization for mounting a phishing attack) contacted twitter employees working remotely from their homes and collected their credentials impersonating as twitter IT administrators.
Using these credentials, they gained access to administrators’ tools and using them reset the twitter accounts of these famous personalities and posted messages promoting the scam.
As a result, twitter users transferred nearly $180,000 in Bitcoin into the scam accounts. When the scam unearthed, twitter’s share prices tonked by 4%.
CASE 3: Leakage of personal data due to employees negligence
In May 2022, hackers managed to access the full names, email addresses, phone numbers, and corporate IDs of Verizon employees, per a report by Motherboard.
The information was gained, according to the hacker, when they persuaded a Verizon employee to grant them remote access to their corporate terminal. This appeared to be a simple task, as the hacker just pretended to be an inside support employee.
“These employees are idiots and will allow you to connect to their PC under the guise that you are from internal support,” hacker told Motherboard.
The hacker confirmed that they reached out to Verizon demanding $250,000 in ransom to keep the sensitive employees data intact.
The official response of Verizon to the whole episode confirms the attack.
A fraudster recently contacted us threatening to release readily available employee directory information in exchange for payment from Verizon. We do not believe the fraudster has any sensitive information and we do not plan to engage with the individual further. As always, we take the security of Verizon data very seriously and we have strong measures in place to protect our people and systems.
A Quick Note:
If you keep your system updated with the latest software patches and implement services such as IT Asset Management (which helps with taking a snapshot of your system and all of its memory that in turn help identify the breach and any files that were infected) and Secure Endpoint Management (securing your organization’s endpoints and proactively protecting against future attacks), you would be able to fix the weakest link in the cybersecurity and the unfortunate incident of ransomware could be avoided.
2. Criminal or Malicious insider:
A malicious Insider is one who has legitimate and privileged access to the company’s digital assets and data and abuses this privilege to steal trade secrets or sensitive information for personal profit.
He/she can be an employee or a former employee, or even a disgruntled one or a trusted business partner or contractor.
According to the Insider Data Breach survey 2019 commissioned by Egress, 61% of the cybersecurity leadership believe that malicious insiders pose a serious threat.
The Ponemon Institute report found that nearly 23% of the threats came from such malicious or criminal insiders and cost $4.08 Million annually.
Protecting organizations against such threats is a huge challenge as it is difficult to determine when users are doing their job or acting with criminal intent.
CASE: In May 2012, General Electric was bidding for a contract for calibration of turbines with a major power company in Saudi Arabia.
To its utter surprise, it found that a competitor had emerged whose bid was much lower but the costs very similar to its own.
It was shocking to find that the competitor was a company in Canada by Jean Patrice Delia, one of its employees.
Delia, a performance Engineer for over 8 years at GE had taken a sabbatical in 2009 and returned in a slightly different role in 2011.
Using his privileged access to the company’s confidential data he started downloading sensitive information including trade secrets and marketing and pricing data.
He had managed to steal important commercial data from the company so that he could compete with his employer and win those bids.
GE had not only lost many of its tenders for turbine calibration services but also much valuable information which it had painstakingly gathered over the years giving the company a unique market advantage.
Why people are the weakest link in cybersecurity?
As humans, we make mistakes all the time. After all, it is human to err. Even the most conscientious employees make mistakes and cybercriminals are just waiting for such an opportunity. But, there are more complex reasons as well.
1. LACK OF AWARENESS
Employees often are unaware that their negligence can cause a serious data breach and damage their company’s finances and reputation.
This is because many companies do not have a coherent policy towards data access and use. Employees may not be aware of the rules, procedures, laws, and processes put in place to secure the data.
2. EASY ACCESS TO CRITICAL DATA
As employees, people have easy access to their company’s networks, digital assets, and sensitive data. It is routine for them to be accessing them for doing their job.
3. PERCEPTION GAP
There is a perception gap between the leadership and employees regarding what data or information they can access or share and what they cannot.
This had led to too many people accessing information unrelated to their jobs. In fact, one survey found that nearly 65% of the employees had accessed information unrelated to their jobs.
4. PRIVILEGED ACCESS
Most companies and organizations provide privileged access to their employees to sensitive information because it is essential to do so.
But the employees can abuse such privileged access for personal gain.
5. PERSONAL DEVICES
Too many companies allow their employees to perform their tasks on their devices. This makes it possible for employees to transfer critical data onto their devices and leak them either intentionally or unintentionally.
Multiple devices make it much more difficult to control the information as there are too many footprints of the same information which so many people can view and edit.
6. MIGRATION TO CLOUD
With much of the company data migrating to the cloud and employees and other third parties having easy access to data stored in the cloud has only made the risk of data breach much greater.
A survey with CIOs and CISOs revealed that on average there are 15 to 22 times more cloud applications like storage and collaboration being used in the workplace than those authorized by the company’s IT department.
Worse, most such applications are invisible to the CISOs. The Cisco analysis revealed that the CISOs were aware of only 51 cloud applications running within their organizations while the actual number was 730!
The Covid-19 Pandemic Has Only Made the Situation Much Worse
The Covid-19 pandemic has changed the workplace forever. Hybrid work, Remote work, and work from home are the new norm blurring the lines between the office, living room, and the kitchen.
The pandemic further aggravated the weakest link in the cybersecurity exponentially that was already there due to following factors:
1. UNSAFE NETWORKS
Remote work means more and more employees are working on public networks or other networks with much lower security layers.
What this means is that they are accessing their company’s data on unsafe networks. This makes it easier for hacks, and malicious insiders to peer into the company’s data and steal them.
2. USE OF PERSONAL DEVICES
Employees working on personal devices means several security challenges.
- For one, they can transfer confidential information onto their personal computers or laptops and share them with others.
- Secondly, they may not have appropriate and secure software that is necessary to work in a virtual environment.
- Thirdly, they are far more vulnerable to virus threats, hacking, etc.
- Since many family members, especially kids, share the same computers, they may inadvertently delete important information or share them with others.
- Another significant threat is that employees leave their devices unattended which increases the risk of accidental loss of information.
Given the risks of Remote working, it did not take long for cybercriminals to take advantage of the situation. An Interpol Assessment report on the impact of Covid-19 showed a very significant increase in cybercrime during the pandemic.
The key findings of the report are:
- Increased online scams and phishing deploying covid themes phishing emails, impersonating government and health officials.
- Increased use of Disruptive Malware targeting critical infrastructure and health institutions. The agency reported a spike in the number of ransomware and malware attacks in the first 3 months of the pandemic.
- There was an increase in the deployment of Data Harvesting Malwares. Using covid-19 related information as a lure, cybercriminals infiltrated networks to steal data or divert money.
- The rampant misinformation during the pandemic made it easier for criminals to indulge in cyber attacks.
There is an urgent need to address this problem as Remote work is likely to be the future. While technology is important, educating employees on cybersecurity, especially in remote work environments can do much to improve the security of organizations.
How do we strengthen the weakest link in cybersecurity?
The sheer variety and complexity of Insider Threats pose a huge challenge to organizations. In fact, it is a nightmare for CISOs and other cybersecurity professionals.
However, with the right deployment of technology, strategy, and processes, much of the insider threats can be effectively deterred.
1. EDUCATION & AWARENESS TRAINING
Per a report by IT Security Risks Survey 2017, global data; careless actions like misconfiguring systems and components or clicking on a phishing email link by employees are the major cause of cyberattacks.
So it is critically important to make them aware of the impacts of their actions. One can do address this through an awareness training program that is both relevant and engaging.
Making employees aware of the security issues is the first step. But that is not enough. Their training and education have to be translated into everyday behavior. One can achieve this only by building a security culture within the organization.
Even if the employees know of the mistakes they have made, most do not report them.
In fact, most hide them fearing reprimand. So it is imperative to put a transparent reporting system making it easier for the employees to report.
2. POLICY OF LEAST PRIVILEGE
Easy and privileged access to a company’s network systems and sensitive information to the employees increases the risk of falling prey to cybercriminals looking to exploit them or for malicious insiders to misuse or abuse them.
So, it’s important to put in place a policy of least privilege which ensures that users are given privileged access to the data they need to perform their tasks.
3. MULTIFACTOR AUTHENTICATION
Once privileged users are identified, it is important to implement strict authentication controls beyond the current user ID and password combinations. Multi-Factor Authentications are one way ahead. They should be made mandatory.
4. DETECTING INSIDER THREATS
While prevention is the goal of cybersecurity policy, it may not be possible to prevent all attacks. So it is important to put in place technologies and tools and processes that help detect the threats.
a) User Behaviour Analytics
The best way to detect an insider threat and fix the weakest link in the cybersecurity chain is to constantly monitor user behavior and generate alerts when suspicious activity takes place.
This will help us keep a tab on users accessing sensitive files; moving, copying or modifying files.
Sophisticated platforms using AI and Machine learning technologies are making it possible for us to monitor, detect, generate an alert and deter such attacks.
b) Permission Changes
It is important to monitor any changes to permissions given to privileged users which may result in providing unnecessary access to sensitive data.
Time to strengthen the weakest link in cybersecurity with Cyvatar.ai
We already have seen that the source of cyber threats could be both internal and external. Since organizations are primarily concerned about what’s visible externally, internal people’s threat is always overlooked and the organizations pay the price.
But you don’t have to be among those organizations who become complacent with their typical external cyber protection.
Invest time and resources in identifying the insider threats that pose a more serious vulnerability to your organization, by implementing cyber technology that mitigates the internal threats.
Our managed services provide advanced cyber tools that give you a secure workspace and peace of mind. With IT Asset Management and Secure Endpoint Management, you can rest assured that your weakest link is going to be an asset.
Still not sure where to start? Connect with us and let us do the dirty work for you.
