KRI (Key Risk Indicator): Understanding KRI and why is it important?

KRI (Key Risk Indicator): Understanding KRI and why is it important?
Cyvatar | 06/27/2022You have a service level agreement (SLA) with a vendor that there will be a 99.999% uptime guarantee. That’s a downtime of fewer than 5 minutes and 15 seconds in a year.
If you go back on this promise, it doesn’t look good for your business. You might incur penalties too. No business wants this. This is where Key Risk Indicators (KRI) are beneficial.
What are Key Risk Indicators?
Key risk indicators are predictors of unfavorable events that can negatively affect organizations. Businesses get an opportunity to quantify and proactively monitor the level of risk by establishing KRIs. It provides visibility into the organization’s risk and control environment and processes.
There is no right or wrong answer to how many KRIs an organization should have. Consider the number and nature of the key risks identified, the data availability needed for the KRIs, the cost of extracting the data, and the intended audience.
Understanding KRIs and how they can affect your organization’s day-to-day operations is an aspect that leaders should be mindful of.
KRIs could be quantitative that focus on numerical data and provable facts based on results from mathematical models and methods of analysis or qualitative that focus on facilitating things like sensitivity analysis by predicting probability-based outcomes.
KRIs can be divided into four categories based on the types of risk:
- Financial
These metrics help quantify market risk, regulatory changes, or competitive risk. Banking KRIs are common: they include budget changes, acquisitions, or changes in strategic goals.
- Operational
They look at risks that will arise on a day-to-day basis because of a security breach or a malfunction. The operational KRIs could range from poor internal controls to process inefficiencies, leadership changes, and internal failures.
- People
These KRIs measure employee retention rates, customer churn, labor shortages, customer satisfaction, etc. They are most commonly used by HR departments or companies that deal with recruitment or staffing.
- Technological
Most industries have tech-related KRIs. They measure data breaches, system failures, or regulatory changes.
What is the purpose of a KRI?
KRIs play an influential role in risk management. If there are no KRIs, the possibility of the organization being subject to events that could cause huge damages is highly likely.
KRIs ensure that the risks are identified, monitored, and remediated before they become a mess.
If an organization provides email marketing automation solutions, an important KRI should be high deliverability. An increase in emails being returned to the sender is an indication that there are problems that need to be immediately addressed.
Choosing the KRIs for your organization is a task that many find difficult. The internal acceptance of the KRIs is also a key factor.
Everyone in the organization should be informed about the importance of the KRIs, their significance, and how to respond if there are alerts.
Defining and monitoring KRIs gives you a deep insight into the critical threats to the organization. When you understand the risk dynamics, you can apply accurate methods to assess and minimize the risks.
You can set a risk tolerance threshold and trigger reactions if it is crossed. Organizations that regularly monitor the KRIs get an accurate view of the risk trends.
You’ll understand which business lines are vulnerable and which ones need increased monitoring.
Let us look at what else KRIs can help with:
- Quantifying each risk and its potential impact
- Identifying risk exposure relating to the latest risk trends
- Enabling timely risk control and monitoring
- Providing risk benchmarking for a better perspective
- Helping stakeholders receive timely alerts on potential risks
- Developing appropriate risk responses
- Creating a risk management process
Characteristics of good KRIs
When developing KRIs, you must have a detailed understanding of the organization, the industry in which it operates, and the potential risks it may face.
The characteristics of good KRIs include the following:
- Details about the people, processes, technologies, resources, and other aspects important to the success of the organization
- Identifying the risks and threats that the organization faces and how they will impact its day-to-day operations and finances
- Ranking the threats and vulnerabilities in terms of the harm they can cause
- Ranking critical business attributes
- Linking key business attributes to the risks and identifying serious threats
- Should be quantifiable in terms of numbers and percentages
- Approval of the KRIs by stakeholders
- They should be easy to collect, parse, and report on
- You should be able to ratify the way you sourced it, aggregated it, and reported on it
- Must be benchmarkable both internally and to industry standards
Key Risk Indicators examples
Let us look at 10 examples of Key Risk Indicators.
| Risk | Measurable KRI | Why track this risk? |
|---|---|---|
| ISP Failure | Number of ISP outages | If there are a high number of outages, it means that you should change the vendor. Your business can come to a full stop because of outages |
| Data loss | Number of system backup failures | Upgraded software can result in backup failure |
| Unaddressed critical incidents | Time taken to resolve an incident/ Number of critical incidents | If the time taken to resolve critical incidents are high, then the organization’s critical incident procedure needs to change |
| Anonymous data leak | Number of active database administrator accounts | Default admin accounts means if an event occurs, it isn’t possible to point back to the individual |
| Improper security arrangements | Number of users with similar roles but dissimilar security arrangements | Employees may be accessing customer data files that they shouldn’t |
| Malware | Number of employees who click on phishing emails | Test employees with fake phishing emails. Use the results to identify employees who require extra security training |
| Vendor service interruption | Number of applications in the organization without a Service Level Agreement (SLA) | You may be engaging with a high-risk vendor if there is no SLA. They aren’t obligated to adhere to your regulations, thereby interrupting your business. |
| Breach of GDPR compliance | Time to respond to requests for personal data | It can result in serious financial and reputational damage |
| Shared login credentials | Number of concurrent systems using the same login ID | It shows that the employee has shared their login credentials with unauthorized individuals |
| Non-compliance and data breaches | Frequency of review of privileged permissions on IT systems | These accounts are likely to be targeted by cyber attackers to gain access to sensitive data |
How to develop Key Risk Indicators for your business?
Before developing KRIs, you need to understand the company’s goals and vulnerabilities that cause risk. Key risk management is all about identifying the most significant risks. Such risks are the ones that have the highest likelihood of occurring, the ones that will have the most significant impact, or those that are outside your company’s control.
If you have already identified Key Performance Indicators (KPIs), it is easy to create KRIs. The KPIs indicate what matters the most to your organization. It will reduce the time spent on identifying pivotal aspects of the business. The KRIs you choose should also be relevant, measurable, and timely.
The organization should adhere to the following best practices when developing the KRIs:
- Get the leadership’s buy-in and involve relevant stakeholders in the process
- Make sure that everyone is on the same page when identifying key risk indicators
- The information about KRIs and the subsequent process should be available with all of the stakeholders
- There should be a point of support for all stakeholders
- Ensure that the stakeholders are apprised of the latest changes
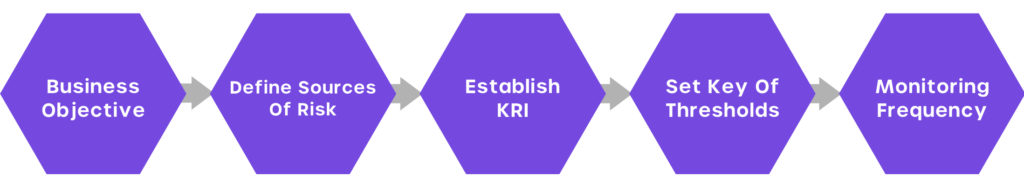
Steps to develop Key Risk Indicators
- Revisit existing metrics: The metrics that you monitor should be regularly reviewed. Conduct a SWOT analysis for your organization to identify, analyze, and document its risk appetite. The metrics should be changed periodically based on the industry.
- Conduct a full risk assessment: Revisit each metric and conduct a full risk assessment to measure your risk appetite. It is carried out to determine how the potential risks affect your goals. Use this opportunity to learn about the possibility of the risk becoming an event, where it might have the most impact, etc.
- Track changes in the control environment: The Internal Control-Integrated Framework (published by the Committee of Sponsoring Organization) ensures the standards, processes, and structures in organizations are properly in place to safeguard your organization.
If there are changes to the processes and controls, it can negatively affect the effectiveness of the control environment and risk exposure.
- Isolate the root causes: When you identify the risks, they have to be prioritized, and each of them will require a unique response based on its priority.
Conduct a root cause analysis to determine the importance of the risk and determine the action that needs to be taken.
- Periodically collect data on KRIs: The data on the KRIs should be collected regularly. The KRIs you choose should be measurable, predictable, comparable, and informational.
- Determine responsibilities: When developing KRIs, ensure that you determine who is responsible for tracking and reporting KRIs, developing risk responses, updating controls, and re-evaluating the KRIs.
Challenges of developing KRIs
Many organizations encounter challenges when developing KRIs because they don’t address the risks associated with their development.
Let us look at some of the challenges in developing KRIs:
- Getting accurate information about the organization can be difficult. In cases where it isn’t available, finding mission-critical activities can become a cumbersome process.
- Organizations might find it challenging to identify the risks, threats, and vulnerabilities and quantify them by severity and impact.
- Getting leadership buy-in for the use of KRIs as an enterprise risk management program is a challenge
- Creating metrics that are measurable and understandable by the leadership
- Building activities to analyze changes in the KRI metrics
- Establishing responses when there are deviations from the KRI metrics
- Additional resources required to develop the KRI framework
- Creating a holistic KRI framework without excluding risks
- Poorly tracking KRIs due to inefficiencies caused by lack of proper resources
KRI VS KPI
Majority of us think that KRI and KPI are the same. Although they are related, they are not the same. They work together to provide firms and their leaders with the measurements they require to strengthen their operations.
| KRIs | KPIs |
|---|---|
| Look forward to the future | Consider past performance |
| Assess and manage risks | Measure performance |
| Focus on probability that an organization will achieve goals against the potential risks | Prioritize key goals and monitor anticipated performance |
Assess and manage potential risks with Cyvatar
To keep the focus on the critical risks, KRIs should be tied to a KPI and a business goal, and they should be prioritized.
Designing and setting up KRIs for your organization is as pivotal as anything else. Creating an efficient set of KRIs will show you the potential risks that your organization carries. Using KRIs effectively also necessitates having the correct risk management framework in place.
You stand to benefit when you examine the KPIs regularly. Leverage technology to enhance your organization’s risk management approach to complement the existing risk identification methods to get the maximum benefits.
| Start with the Freemium plan that provides a monthly external vulnerability scan, CIS assessment, and cybersecurity policies for free! |
